
Bitcoin Dust Attacks: How Privacy Gets Compromised
Understand how dust attacks exploit Bitcoin's UTXO model to track wallet owners when tiny outputs get combined with other funds in transacti…
Step-by-step to Sovereignty & Lightning Network


Understand how dust attacks exploit Bitcoin's UTXO model to track wallet owners when tiny outputs get combined with other funds in transacti…
Choose the right operating system and hardware for Bitcoin node deployment, comparing Ubuntu Server, Debian, and purpose-built node OS optio…

Weigh the trade-offs between KYC and non-KYC Bitcoin acquisition, examining how identity-linked purchases create permanent surveillance reco…

Break down the costs of Bitcoin privacy tools like CoinJoin and mixing services, analyzing fee structures and their real privacy-to-cost rat…

Build secure Bitcoin wallet infrastructure by combining full nodes, electrum servers, and hardware wallets into a modular self-sovereign sta…

Verify your Bitcoin holdings privately using extended public keys, watch-only wallets, and self-hosted nodes without exposing private keys. …

Advanced Bitcoin cold storage privacy strategies covering personal node setup, Tor networking, and transaction privacy techniques. …
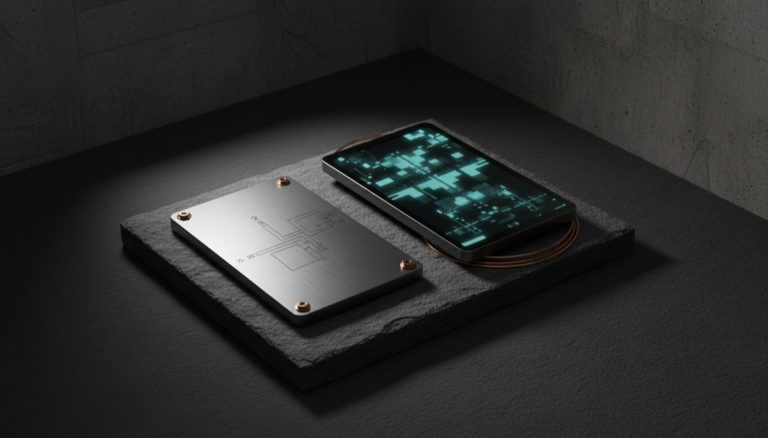
Compare digital and physical seed phrase backup methods. Covers metal plates, encrypted storage, geographic distribution, and durability tes…

Compare CBDCs and Bitcoin on privacy, monetary control, and individual sovereignty, examining why government digital currencies threaten fin…

Bitcoin Node Network Discovery and Access: run and maintain your Bitcoin node effectively. Hardware, software, and security considerations c…