
How to Test Your Seed Phrase Backup
Verify your seed phrase backup actually works before an emergency. Covers safe testing methods, passphrase checks, and common restoration mi…
Step-by-step to Sovereignty & Lightning Network

Comprehensive guides on protecting your Bitcoin: cold storage, seed phrase security, multisig setups, hardware wallet reviews, and operational security best practices.

Verify your seed phrase backup actually works before an emergency. Covers safe testing methods, passphrase checks, and common restoration mi…
Compare Shamir Secret Sharing and multisig for Bitcoin backup security. Covers threshold schemes, recovery complexity, and real-world trade-…

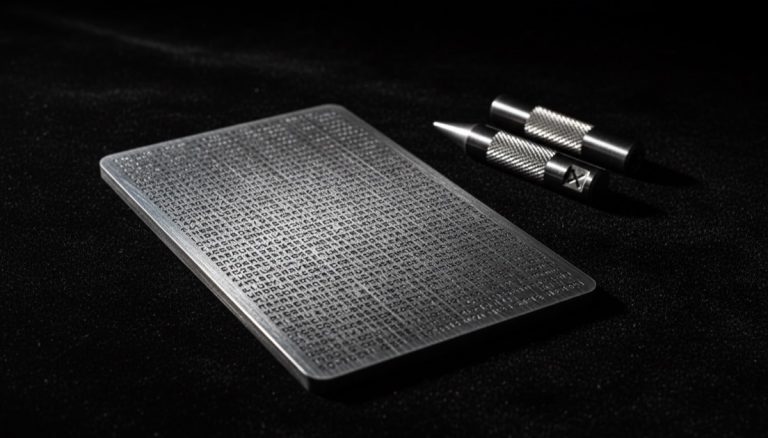
Protect seed phrases with metal backup solutions. Covers steel plates, titanium options, engraving versus stamping, and fire and flood resis…

Configure a 2-of-3 multisig Bitcoin wallet for enhanced security. Covers key distribution, signing workflows, and recovery scenarios. …

Bitcoin security 2026 in review: exchange hacks, quantum-resistant wallets, and Silent Payments progress. Key events every holder should kno…

Bitcoin Self-Custody Checklist 2027: essential knowledge for Bitcoin self-custody. Practical guide with expert tips and proven strategies. …

Plan Bitcoin inheritance using multisig setups. Covers key distribution to heirs, time-locked recovery paths, and legal considerations. …

Seed Phrase Inheritance: protect your Bitcoin recovery words properly. Storage methods, common mistakes, and best practices. …

Set up a multisig wallet using Sparrow desktop software. Covers key generation, PSBT signing workflows, and coordination with hardware devic…

Protect your Bitcoin with proper seed phrase management. Covers BIP39 word lists, metal backup methods, engraving tips, and inheritance plan…

Bitcoin multisig wallets explained from basic 2-of-3 setups to advanced configurations, eliminating single points of failure in your custody…

Seed phrase passphrase (25th word) explained with setup steps on popular hardware wallets, security benefits, and critical risks to avoid. …

Cryptosteel vs Billfodl compared on material quality, fire resistance, capacity, and usability to find the best metal seed phrase backup. …

Seed phrase vs private key differences explained — how the BIP39 hierarchy works and why your backup strategy depends on understanding both.…
Understand the 24-word recovery phrase used in Bitcoin wallets. Covers BIP39 word lists, generation process, secure storage, and common mist…

Add a passphrase (25th word) to your seed phrase for extra security. Covers plausible deniability, hardware wallet integration, and recovery…

Compare cold storage and hot wallets to balance security with convenience. Covers private key isolation, attack vectors, and layered custody…

Compares truly FOSS Bitcoin hardware wallets against source-viewable alternatives in 2026, weighing transparency, security, and community tr…

Side-channel attacks extract private keys via power analysis, electromagnetic emissions, and timing leaks. Learn how they threaten hardware …

Update hardware wallet firmware safely without risking funds. Covers verification steps, seed phrase red flags, and proper backup procedures…

Verify Bitcoin Core downloads with PGP signatures and SHA256 checksums. Covers reproducible builds, trusted sources, and release authenticat…

Host your own Bitcoin server and web services for full digital sovereignty. Covers bandwidth limits, security hardening, and self-hosting tr…

Recover a multisig Bitcoin wallet after key or device loss. Covers 2-of-3 setups, xpub coordination, and preserving wallet structure for saf…

Weigh the security gains of multisig Bitcoin wallets against added complexity. Covers key separation, passphrases, and operational trade-off…

Compare single-signature and multisig cold storage setups, including 2-of-3 and 3-of-5 configurations, key management, and backup strategies…

Protect your Bitcoin seed phrases from fire, flood, theft, and degradation with durable metal backups, geographic distribution, and redundan…

Understand the technical complexities of Bitcoin multisig, from xpub management and derivation paths to hardware compatibility and recovery …

Learn how the Dark Skippy attack exploits weak nonce generation in compromised hardware wallet firmware to extract your master private key f…

Understand how BIP-85 lets you derive unlimited child seed phrases from one parent seed using BIP-32 root keys, simplifying multi-wallet bac…

Diagnose Lightning Network wallet failures including routing issues, channel liquidity problems, and complications from Lightning-to-Liquid …

Bitcoin Mining UTXO and Privacy Management: protect your financial privacy with proven techniques. Practical tools and strategies for Bitcoi…

Understand multisig Bitcoin wallet architecture including M-of-N key schemes, BIP32 key generation, and critical backup recovery procedures.…

Set up a Bitcoin multisig wallet using multiple hardware wallets. Covers 2-of-3 and 3-of-5 configurations, device selection, and key managem…

Best practices for designing Bitcoin cold storage setups, from single-sig hardware wallets to multisig configurations and threat modeling. …

Compare Lightning Network and Liquid sidechain as Bitcoin Layer 2 scaling solutions, covering transaction speed, throughput, and trade-offs.…

Examine Bitcoin security from air-gapped signing devices to quantum computing threats, including how Shor's algorithm could impact public ke…

Set up Bitcoin multisig wallets with M-of-N signing schemes enforced at the protocol level, using multiple hardware wallets for distributed …

Explore Lightning Network architecture including payment channels, smart contracts, and time-locked transactions, with a focus on privacy im…

Build a DIY air-gapped Bitcoin signing device using single-board computers, with guidance on eliminating wireless risks and isolating privat…

Analyze how blockchain-based digital identity systems could enable surveillance, and why self-sovereign solutions matter for personal freedo…

Evaluate the risks and techniques of memorizing Bitcoin seed phrases, including mnemonic methods, cognitive science principles, and security…

Manage Bitcoin seed phrases safely when migrating from hot to cold storage, with critical rules on key isolation and hierarchical determinis…

Understand how multi-signature Bitcoin custody evolved from single-key storage, including 2-of-3 setups and hardware wallet integration. …

Learn secure methods for migrating Bitcoin from paper wallets to hardware wallets, with key security steps for cold storage transfers. …

Design robust backup strategies for multisig Bitcoin wallets, including seed phrase distribution and defense against physical coercion attac…
Compare digital and physical seed phrase backup methods. Covers metal plates, encrypted storage, geographic distribution, and durability tes…

Bitcoin Node Network Discovery and Access: run and maintain your Bitcoin node effectively. Hardware, software, and security considerations c…

Plan your Bitcoin inheritance with cold storage solutions that balance strong security and family accessibility for emergency fund recovery.…

Bitcoin Cold Storage and Multisig Security: secure your Bitcoin with multi-signature protection. Setup, best practices, and common pitfalls …

Bitcoin Node Security and Decentralization: run and maintain your Bitcoin node effectively. Hardware, software, and security considerations …

Multisig wallets require multiple private keys to authorize Bitcoin transactions, providing institutional-grade security through distributed…

Master Lightning Network channel liquidity by balancing local and remote capacity, acquiring inbound liquidity, and working with LSPs. …

Modern air-gapped hardware wallets now feature QR scanning, NFC, and full keyboards for secure seed entry while maintaining complete device …

Compare seed phrase backup solutions including Shamir's Secret Sharing, which splits your seed into distributed shares requiring a threshold…

Compare Bitcoin cold storage self-custody with yield platforms and trading services. Understand the hidden risks of chasing crypto returns. …

Explore how Bitcoin cold storage reduces liquid supply, creates virtuous scarcity, and strengthens the network's store-of-value proposition …

Explore how 256-bit entropy secures Bitcoin seed phrases and weigh the pros and cons of dice rolls versus hardware random number generators.…

Master Bitcoin self-custody with hardware wallets, from seed phrase generation and BIP39 standards to multi-layer security for your private …

Examine the risks behind Bitcoin yield products including Layer 2 protocols, wrapped tokens, and lending platforms that add counterparty exp…

Analyze Lightning Network scaling hurdles including channel liquidity, routing complexity, and the requirement for pre-funded payment channe…

Secure your multisig wallet by properly verifying extended public keys (xpubs) during setup to prevent compromised signing devices and fund …

Learn how wallet passphrases create entirely separate hidden wallets through HMAC-SHA512 cryptographic transformation of your seed phrase. …

Discover how multisig M-of-N wallet schemes distribute signing authority across devices to eliminate single points of failure in Bitcoin sec…